
15
NovemberDownload Bootloader File

15
NovemberBurn Hex File of Bootloader to Microcontroller

15
NovemberDrivers

15
NovemberFirst EXAMPLE Blink A LED

15
NovemberNow Build your own Pinguino

15
NovemberBonus Lecture: Manufacture a Professional PCB - By PCBWay
15
NovemberWho We Are
15
NovemberIntroduction
15
NovemberWhat is Ultiboard and Why you should use it
15
NovemberDownload and Install Multisim and Ultiboard
15
NovemberMultisim User Interface Explained
15
NovemberDrawing a Simple Schematic
15
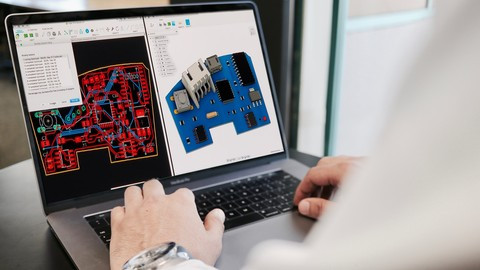
NovemberCreate your first PCB Design
15
NovemberCreate a Schematic for Arduino UNO Shield
15
NovemberCreate a PCB for Arduino UNO Shield
15
NovemberArduino Boards Templates for Multisim
15
NovemberMultisim Templates for Custom Arduino Shields
15
NovemberCreate PIC Microcontroller Breakout Board Schematic
15
NovemberCreate PIC Microcontroller Breakout Board PCB
15
NovemberLed Controller Circuit Schematic and PCB Design
15
NovemberIntroduction
15
NovemberWho We Are?
15
NovemberThings Used in this Project - Hardware
15
NovemberThings Used in this Project - Software and Web Editor
15
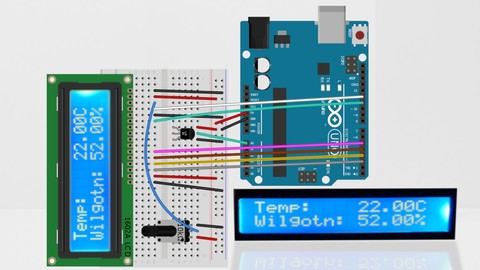
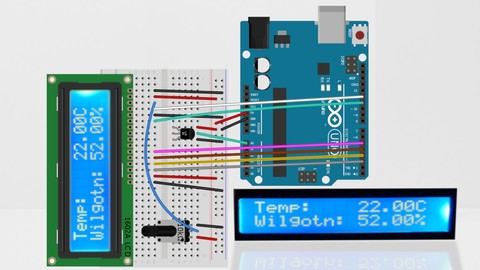
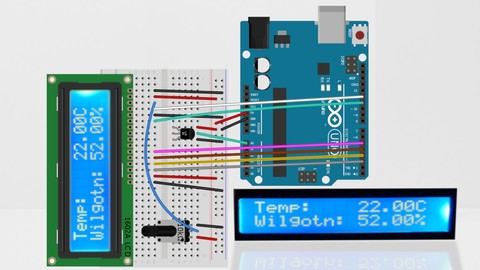
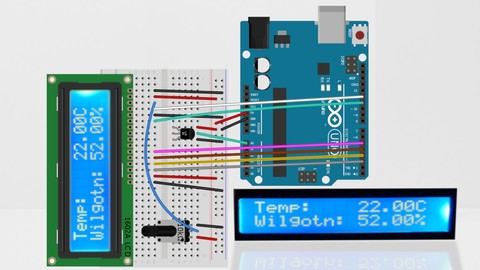
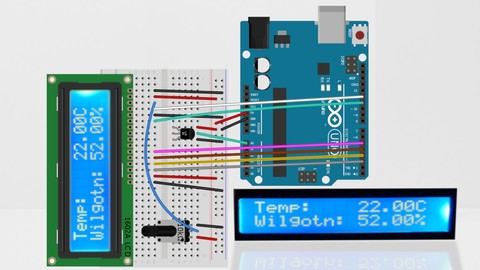
NovemberTemperature and Humidity Sensor Wiring
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231